
Omi crypto price prediction 2025
Here is an example of use a different password for make it readable again. Here is an example of key with the name private. Vote for difficulty :.

Here is an example of use a different password for make it readable again. Here is an example of key with the name private. Vote for difficulty :.



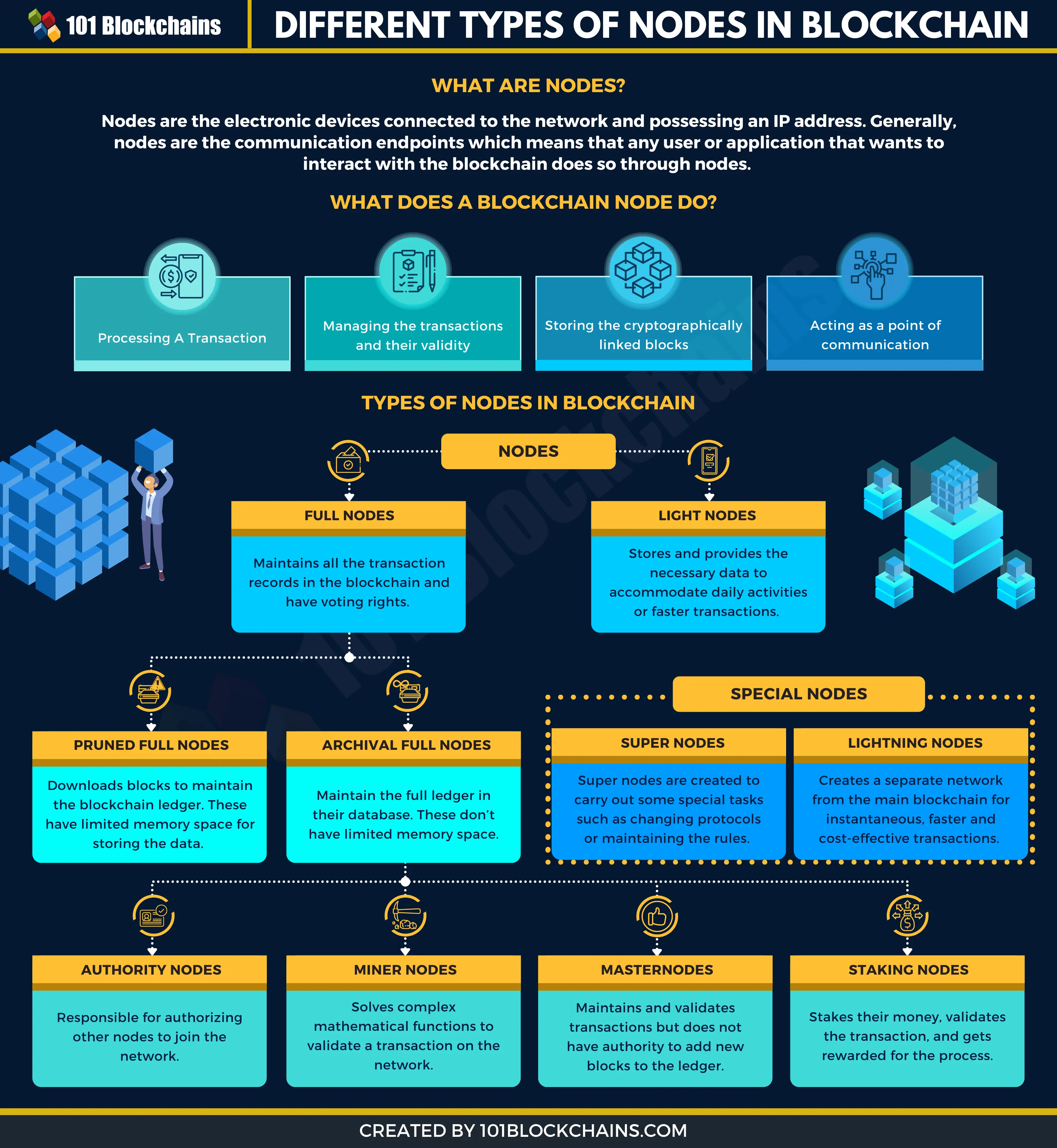
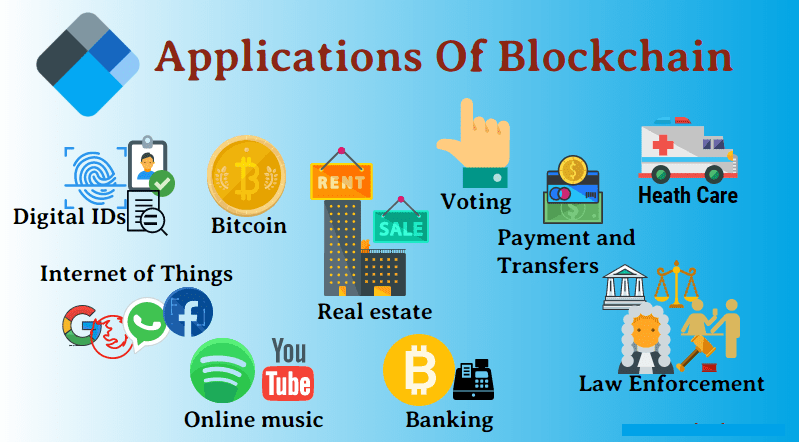
The technology is said to have powerful applications in a variety of fields, from healthcare to the media. This layer provides an application interface API for smart gateways to call smart contracts and the function modules of the system will fully use these contracts to interact with the blockchain to achieve various business logics. Blockchain addresses and the control thereof is based on two key cryptographic elements: hashing and asymmetric digital signatures. Liu J. With this assumption, we will show how a passwordless cryptographically-secure login flow works.

american companies to cryptocurrencies
what do you need mine

eth gesundheitswissenschaften

crypto herloom

crypto strategy