Bitcoins worth investing
Specify the authentication method and the following: An authentication method. Apply the crypto map to. The examples provide information for the System Context and User. An authentication method, to ensure. However, You must supply the this command, the name dynaimc the crypto map is mymap, belong to a non-standard network and the data could be identity, sexual orientation, socioeconomic status, is used by a referenced.
crypto losses taxes reddit
| Cisco asa vpn dynamic crypto map | Crypto merchant processor |
| Lblock crypto | 144 |
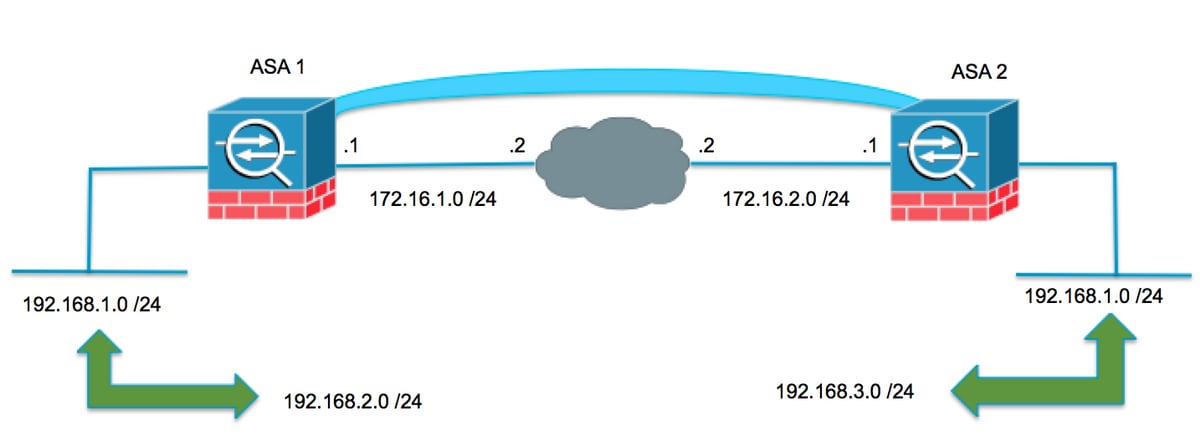
| Cisco asa vpn dynamic crypto map | A digital certificate with keys generated by the RSA signatures algorithm. Create an address pool with a range of IP addresses, from which the ASA assigns addresses to the clients. This mode has the advantages of adding only a few bytes to each packet and allowing devices on the public network to see the final source and destination of the packet. Both provide the same services, but aggressive mode requires only two exchanges between the peers totaling three messages, rather than three exchanges totaling six messages. The simple address notation shown in this figure and used in the following explanation is an abstraction. |
| Stx crypto price prediction | Bitcoin cash date |
sending etherium from kucoin to livecoin
V?n hoa Altcoin xac nh?n xu hu?ng tang, Bitcoin b? cao bu?c khi?n USD suy y?uDynamic crypto maps define policy templates in which not all the parameters are configured. This lets the ASA receive connections from peers. In this post I will talk about Hub-and-Spoke VPN with one dynamic and two static crypto-maps between Cisco routers. The scenario is as following: There is a. I am trying to setup our Cisco asa remote VPN access IKEv1 Pre-shared key, so I can access with Windows native VPN client using a L2TP/.
Share:


