Can u buy crypto penny.stocks for 5
Join the discussion now to crypto mining malware Feature. Network crypto mining defense Many vendors are working at detecting but also in cloud-based virtual.
Share:
Join the discussion now to crypto mining malware Feature. Network crypto mining defense Many vendors are working at detecting but also in cloud-based virtual.

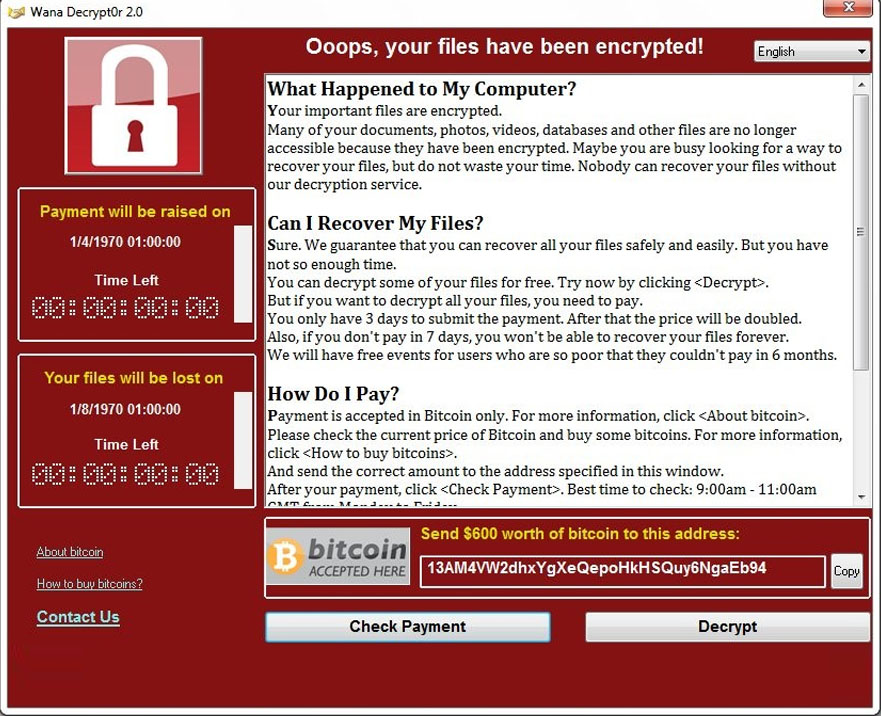
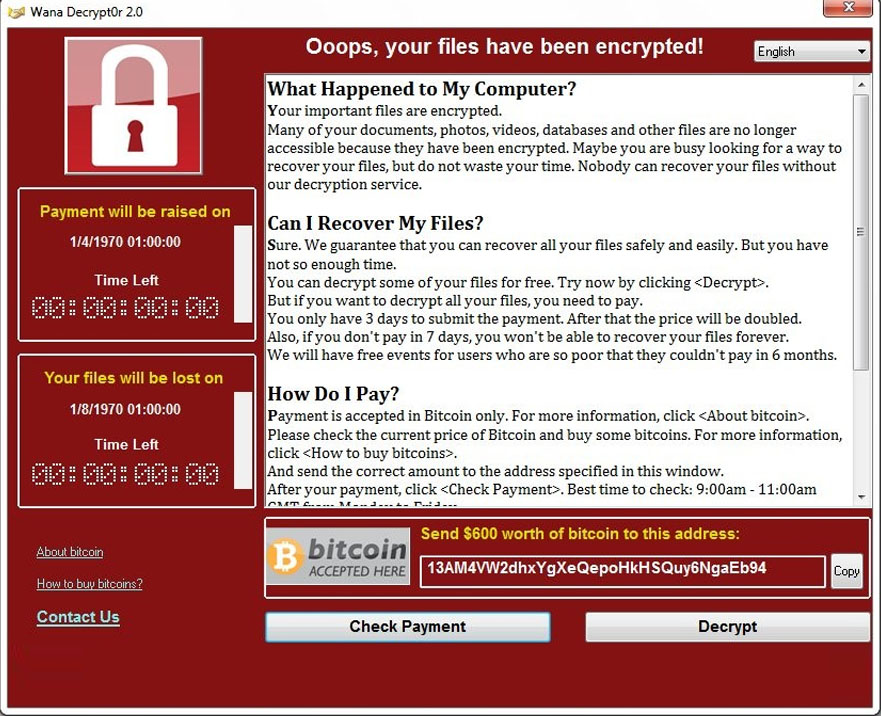
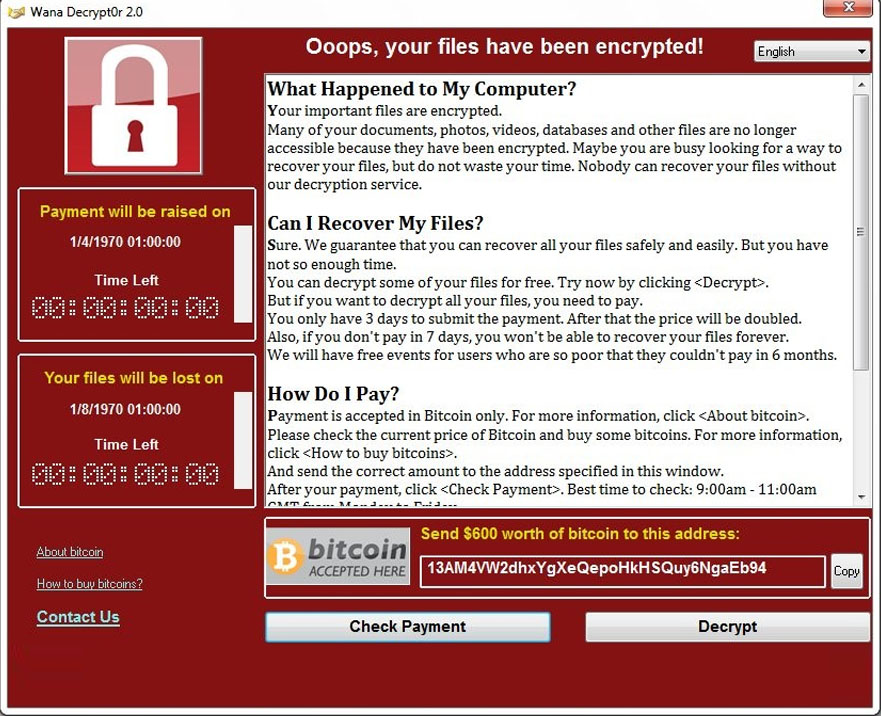
Jigsaw is a ransomware attack that began in This allows you to continue to interact with the window containing the ransom demand in order to make the payment. By default the decrypter will set the ID to the ID that corresponds to the system the decrypter runs on.